Password Hashes — How They Work, How They're Hacked, and How to Maximize Security | by Cassandra Corrales | Medium

Cauliflower Hash Browns | Recipe | Cauliflower, Easy cauliflower recipes, Cauliflower hash brown recipe

How Cryptographic Hash Functions Solve a Very Difficult and Important Problem | by Bennett Garner | Medium

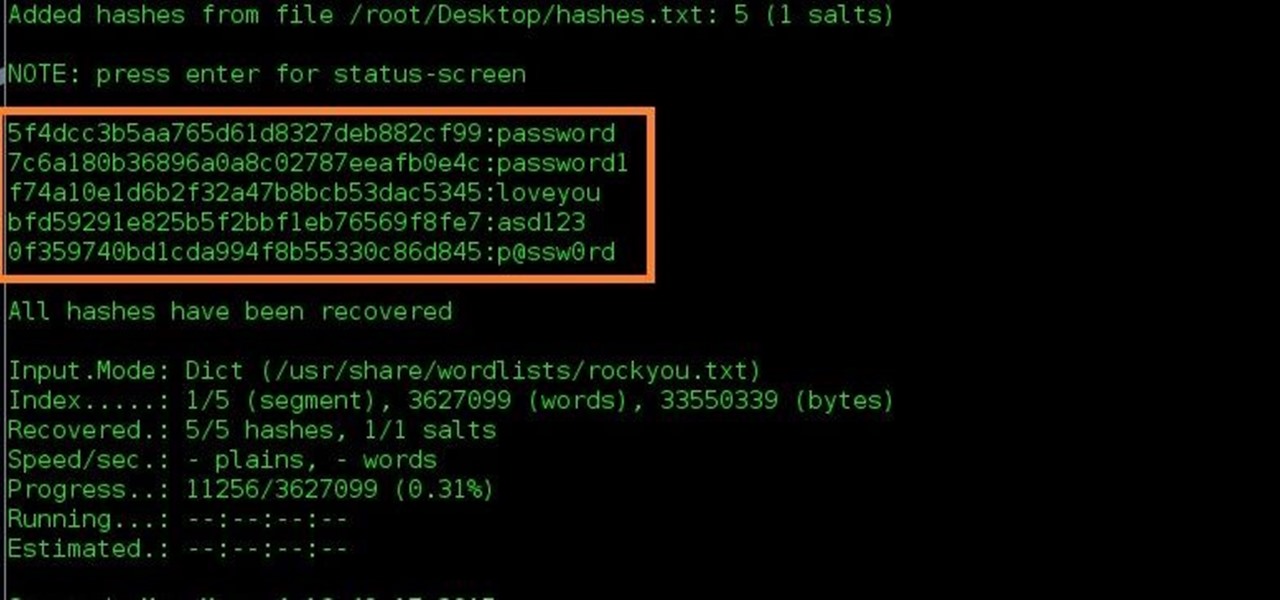
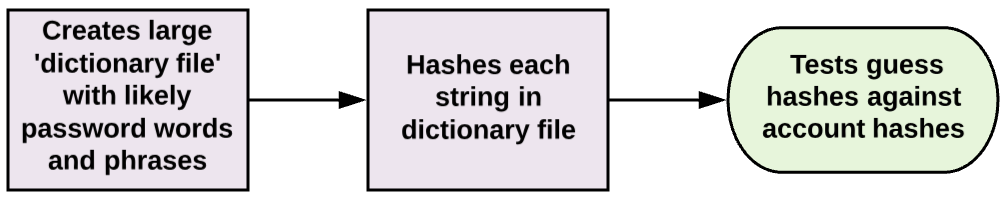
Password Hashes — How They Work, How They're Hacked, and How to Maximize Security | by Cassandra Corrales | Medium

2: A simple depiction of the user authentication process. Evil Eve is... | Download Scientific Diagram




![What Is Cryptographic Hash? [a Beginner's Guide] What Is Cryptographic Hash? [a Beginner's Guide]](https://techjury.net/wp-content/uploads/2020/06/hash-functions-speed-1024x753.png)